
May 23, 2023
In today's digital age, securing sensitive data is a top priority for businesses of all sizes. With cyber attacks becoming increasingly sophisticated, it's essential to have robust security measures in place to protect your organization's assets and reputation. One of the best ways to achieve this is by leveraging the advanced security technologies available in Microsoft Azure Active Directory (AD).
Azure AD is a cloud-based identity and access management (IAM) solution that allows organizations to manage user identities and control access to their cloud resources. It provides a comprehensive suite of security features to help businesses safeguard their data and applications against threats, both internal and external.
In this blog post, we will explore some of the key security technologies available in Azure AD and how they can be used to enhance your organization's security posture.
Conditional Access Policies
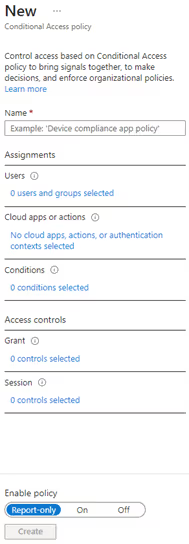
One of the most powerful security technologies in Azure AD is Conditional Access. It allows you to define policies that determine who can access your cloud resources and from which devices and locations. By setting up Conditional Access policies, you can enforce stricter security controls based on various conditions, such as the user's location, device state, network location, and more.
For example, you can set up a policy that requires multi-factor authentication (MFA) for users accessing your resources from outside your corporate network. Or, you can require specific device compliance checks before granting access to certain applications or data.
Conditional Access policies are highly customizable and can be applied to different scenarios, such as protecting Office 365 applications, Azure resources, or custom applications. They provide a granular level of control over access to your cloud resources, reducing the risk of unauthorized access.
A new conditional access policy can be added in Azure Active Directory, Security settings. Access can be granted, or blocked, for specific users and groups, certain applications or authentication contexts, locations, or even conditions, like device compliance or operating systems update status.
Identity Protection
Identity Protection is another security technology available in Azure AD that helps you detect and mitigate identity-based threats. It provides a set of tools and insights to help you monitor user activities and identify suspicious behaviors that may indicate a compromised account.
For example, Identity Protection can alert you when a user tries to sign in from an unfamiliar location or device, or when their account shows signs of suspicious activity. It can also recommend remediation actions to take, such as resetting the user's password, blocking access, or requiring multi-factor authentication.
Identity Protection is especially useful in preventing identity-based attacks, such as phishing, password spray, or brute-force attacks. By monitoring user activities and detecting suspicious behaviors, you can quickly respond to potential threats and protect your organization's sensitive data.
Azure Information Protection
Azure Information Protection (AIP) is part of Microsoft Purview Information Protection. Microsoft Purview Information Protection helps you discover, classify, protect, and govern sensitive information wherever it lives or travels. It provides a unified platform for managing data protection policies and enforcing data protection rules across your organization.
With AIP, you can define policies that automatically apply labels to your documents and emails based on their sensitivity level. You can also apply protection rules that prevent unauthorized access, such as preventing users from copying, printing, or forwarding sensitive data.
AIP integrates with other Microsoft technologies, such as Office 365 and Azure Rights Management, to provide a comprehensive data protection solution. It helps you keep your sensitive data secure, even when it's shared with external parties or stored in the cloud.
Microsoft Defender for Cloud
Microsoft Defender for Cloud, previously known as Azure Security Center, is a cloud-based security management solution that provides a centralized view of your security posture across your Azure and other public cloud environments, like Amazon Web Services and Google Cloud Platform. It helps you identify and remediate security vulnerabilities, monitor security events, and comply with security standards and regulations.
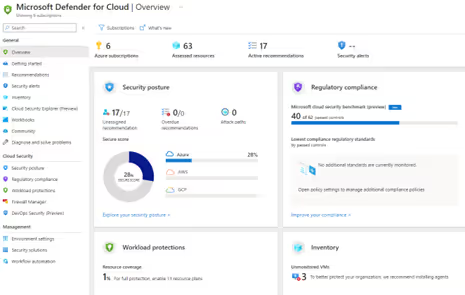
With Microsoft Defender for Cloud, you can get recommendations on how to improve your security posture, such as enabling network security groups or applying security patches. You can also set up alerts to notify you when security events occur, such as failed login attempts or suspicious network traffic.
Microsoft Defender for Cloud provides a wealth of information and insights into your multi-cloud environment's security, helping you stay ahead of potential threats and comply with security standards.
Summary
In conclusion, Microsoft Azure AD offers a wide range of security technologies that help organizations protect their data and applications against various cyberthreats. From Conditional Access policies that control access to cloud resources to Identity Protection that monitors user activities for suspicious behavior, these technologies provide a robust security posture for businesses of all sizes. By leveraging these advanced security features, organizations can enhance their security posture, improve compliance with security regulations, and safeguard their assets and reputation in today's ever-evolving threat landscape.
